Add FusionAuth as an identity provider
Use FusionAuth to give your organization users single sign-on (SSO) access to Aiven.
Step 1: Add the IdP in the Aiven Console
- In the organization, click Admin.
- Click Identity providers .
- Click Add identity provider.
- Select an identity provider and enter a name.
- Select a verified domain to link this IdP to. Users see linked IdPs on the login page.
On the Configuration step are two parameters that you use to set up the SAML authentication in your IdP:
- Metadata URL
- ACS URL
Step 2: Configure SAML on FusionAuth
The setup on FusionAuth has three parts:
- Create an API key
- Generate a custom RSA certificate
- Create an application
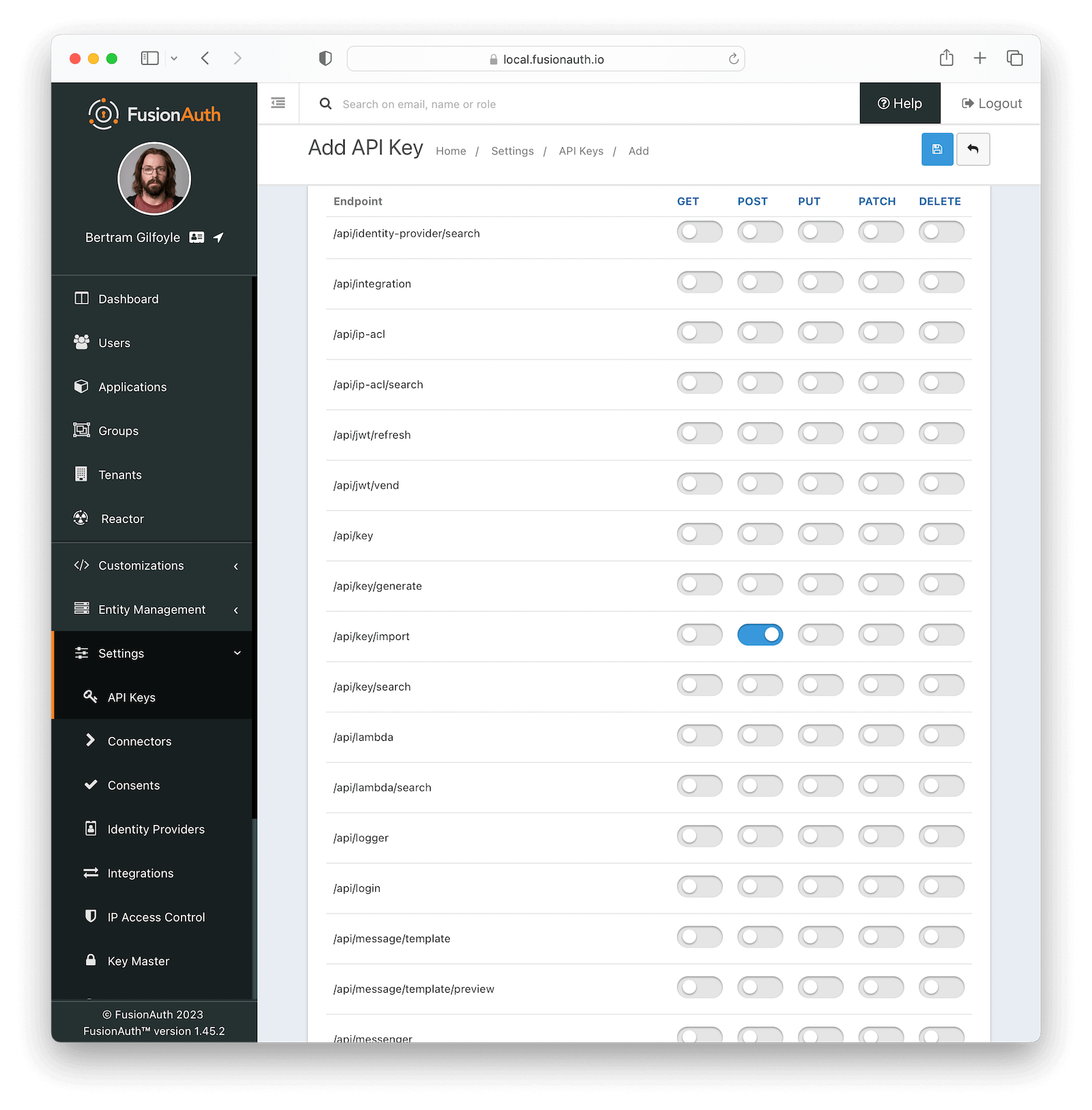
Create an API key
-
In FusionAuth, go to Settings > API Keys.
-
Click the Add icon.
-
Enter a description for the key.
-
In the Endpoints list, find /api/key/import.
-
Toggle on POST.
-
Click the Save icon.
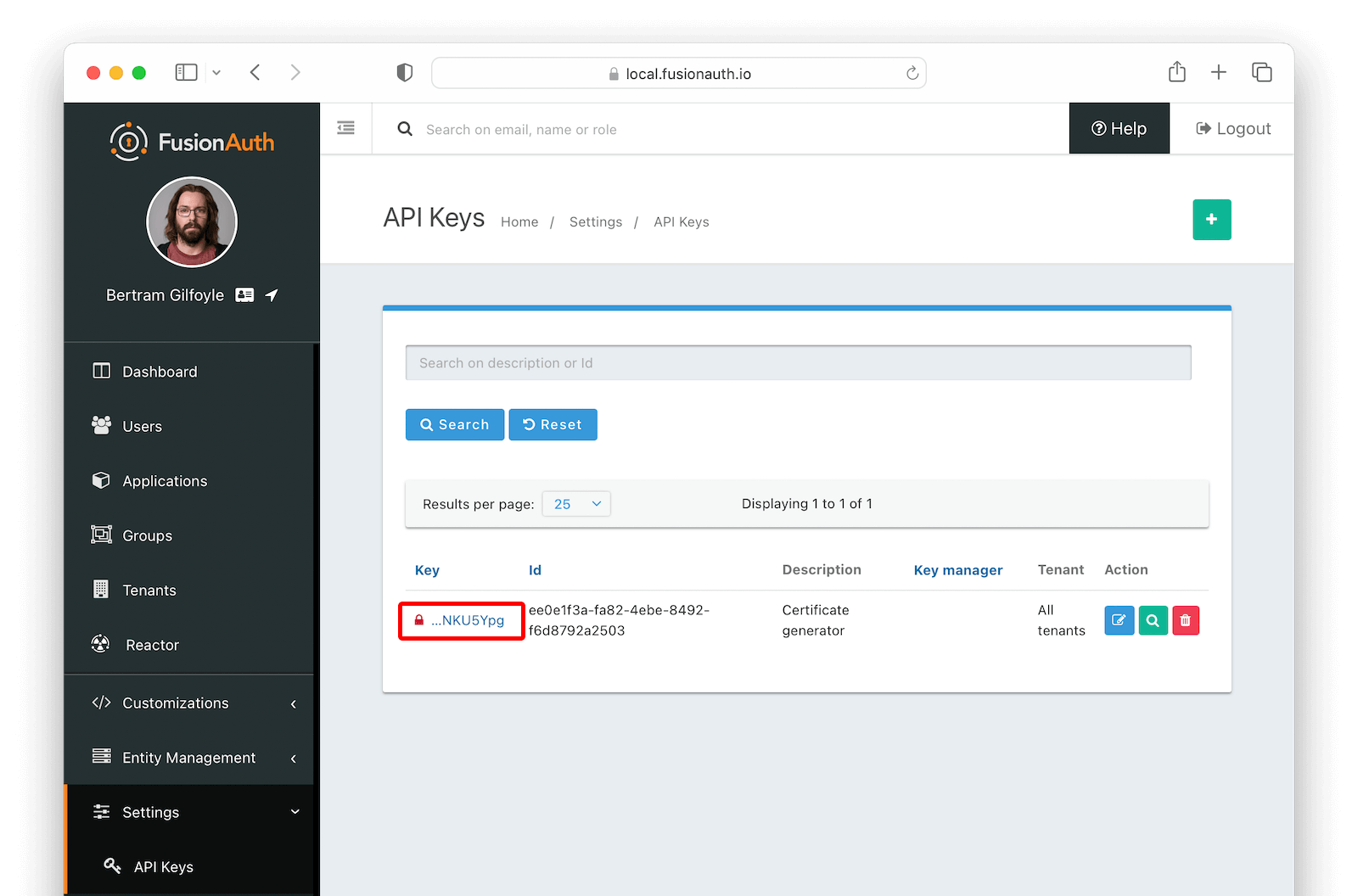
-
On the API Keys page, find your key and click the value in the Key column.
-
Copy the whole key. You'll use this for the script.
-
To clone the FusionAuth example scripts GitHub repository, run:
git clone git@github.com:FusionAuth/fusionauth-example-scripts.git
cd fusionauth-example-scripts/v3-certificate -
Run the
generate-certificatescript../generate-certificate -
Name the key.
-
Copy the generated certificate created by the script.
You now have a certificate in the Key Master in your FusionAuth instance.
Create an application
- In Applications, click the Add icon.
- Enter a name for the application.
- On the SAML tab, toggle on Enabled.
- In the Issuer field, enter the Metadata URL from the Aiven Console.
- In the Authorized redirect URLs field, enter the ACS URL from the Aiven Console.
- In the Authentication response section, change the Signing key to the API key you created.
- Click the Save icon.
- On the Applications page, click the magnifying glass.
- In the SAML v2 Integration details section, copy the Entity Id and Login URL.
Step 3: Finish the configuration in Aiven
Go back to the Aiven Console to complete setting up the IdP. If you saved your IdP as a draft, you can open the settings by clicking the name of the IdP.
- In the IDP URL field, enter the Login URL from FusionAuth.
- In the Entity ID field, enter the Entity ID from FusionAuth.
-
Paste the certificate from the IdP into the Certificate field.
-
Click Next.
-
Configure the security options for this IdP and click Next.
-
Require authentication context: This lets the IdP enforce stricter security measures to help prevent unauthorized access, such as requiring multi-factor authentication.
-
Require assertion to be signed: The IdP checks for a digital signature. This security measure ensures the integrity and authenticity of the assertions by verifying that they were issued by a trusted party and have not been tampered with.
-
Sign authorization request sent to IdP: A digital signature is added to the request to verify its authenticity and integrity.
-
Extend active sessions: This resets the session duration every time the token is used.
-
Enable group syncing: This syncs the group membership from your IdP to the Aiven Platform.
note- The Aiven Platform doesn't create groups with this feature. It only syncs the group membership between the groups in your IdP and the groups you create in Aiven. For user group provisioning, use SCIM.
- User group membership automatically syncs when a user logs in.
- The IdP is the single source of truth. If a group in the IdP doesn't exist in Aiven, it will be ignored. Likewise, if a user is added to a group in Aiven Console but not in the IdP, they will be removed from the Aiven group when the group membership syncs.
-
-
Optional: Select a user group to add all users who sign up with this IdP to.
-
Click Finish to complete the setup.
If you set up a SAML authentication method before and are now switching to a new IdP, existing users need to log in with the new account link URL to finish the setup.
Related pages